The Office of the Australian Information Commissioner (OAIC) has published the first quarterly report on data breach notifications received under the Notifiable Data Breaches (NDB) scheme. The NDB scheme, which came into force on 22 February 2018, requires organisations to report ‘eligible data breaches’ to both the OAIC and any individuals who may be potentially affected by the data breach. Prior to the commencement of the NDB scheme, reporting was recommended but voluntary.
The data provided by the OAIC on which sectors reported data breaches (the most were in health care) and what type of data was exposed (including financial and identity information) is interesting. However, there are two key pieces of information which serve as excellent reminders:
1. Human error was the biggest cause of data breaches.
Human error, such as lost USBs and emails sent the wrong person, are often not properly contemplated in policies and procedures, including training programs, organisational controls and data response plans. They also, of course, can result in an added layer of reputational impact, as there is no malicious third party actor to which blame can be directed (to the extent it ever can).
We also expect that if further insight was given into the other big cause of data breaches, being ‘malicious or criminal act’, there would be a large percentage in that category where it was an ‘inside job’, such as a disgruntled employee misappropriating files or intentionally causing harm.
It is important that organisations don’t solely focus on external threats, where the internal threats, be it an error or intentional malicious act, are the more likely source of issue.
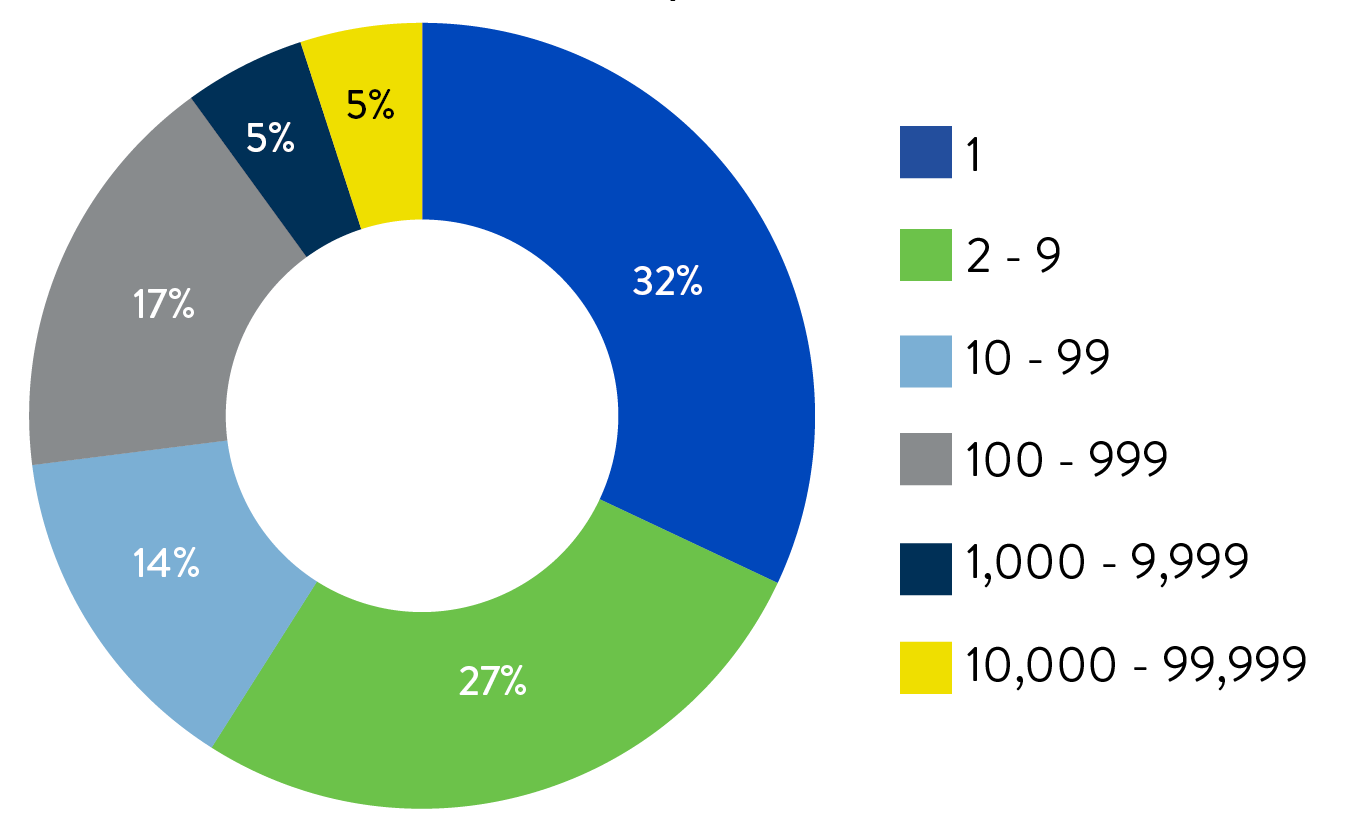
2. The number of impacted individuals, was typically, very low – i.e. less than 10.
The NDB scheme does not have a threshold based on the number of impacted individuals, and indeed 32% of the breaches notified to the OAIC only involved 1 individual.
However, the proportion of breaches which have been notified with so few impacted individuals may reflect that organisations are being conservative in these initial phases of the scheme. This is particularly the case when you consider that a breach is not notifiable in certain circumstances where effective remedial action is undertaken to prevent serious harm to the impacted individual. Usually, there are a range of steps available, particularly when the number of impacted individuals is so low, to effectively prevent such harm.
Please reach out to us if you have any questions regarding steps to take to:
- manage your data assets;
- respond to data breaches, including steps to minimise harm to individuals; or
- otherwise comply with the NDB scheme or the Privacy Act 1988 (Cth).
Further information regarding the nature and type of data breaches reported to the OAIC is set out below:
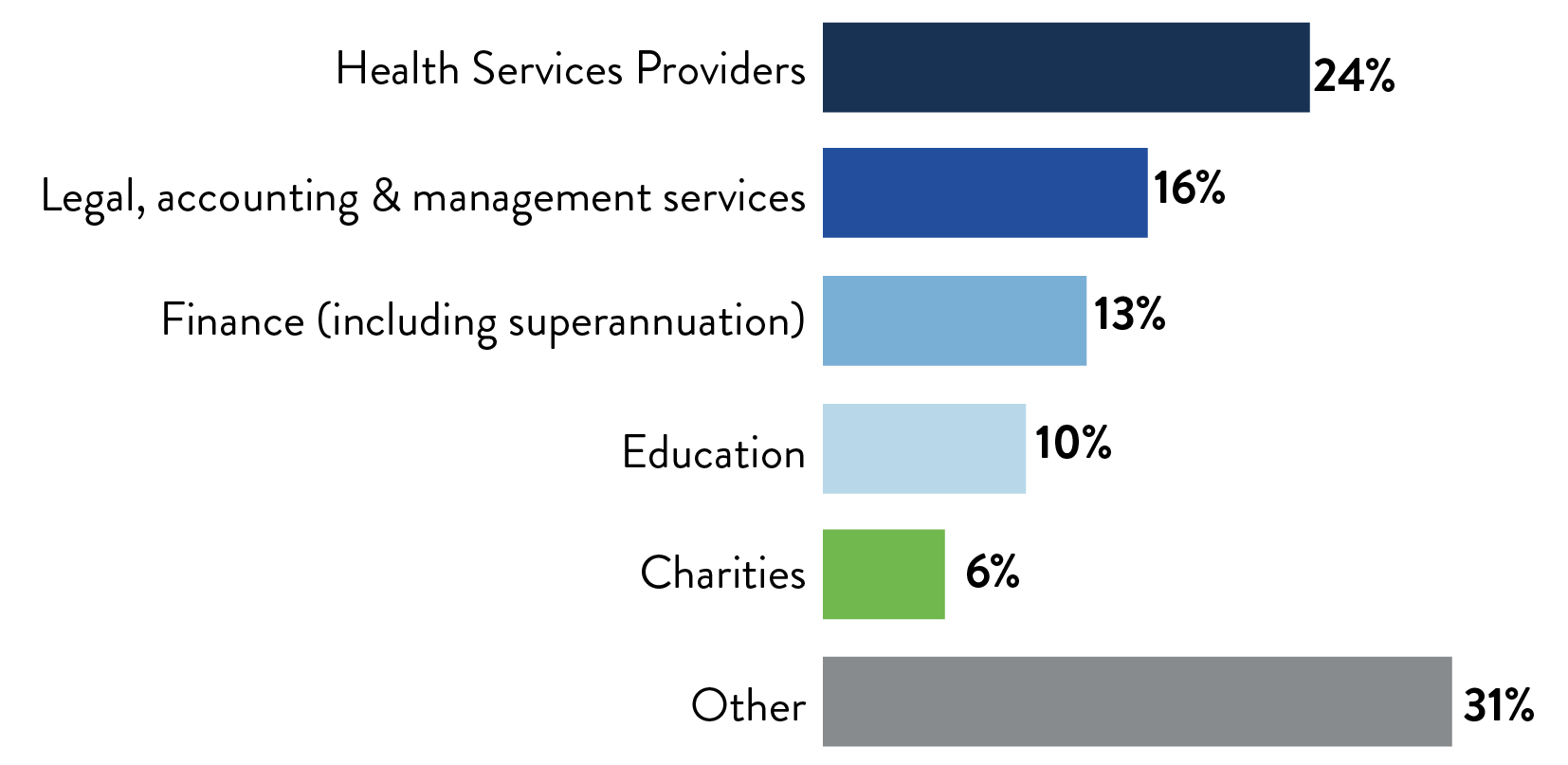
Industries that reported data breaches
According to the report, the OAIC received 63 data breach notifications during the first 6 weeks of the NDB scheme. This compares to 114 voluntary notifications received by the OAIC during the 2016-17 financial year (i.e. before the NDB scheme came into force).
Health service providers, that is, organisations that provide health services and that hold health information, accounted for 24% of all notifications. The legal, accounting and management services sector followed closely comprising 16% of all notifications, with the finance (including superannuation), education and charities sectors not far behind.
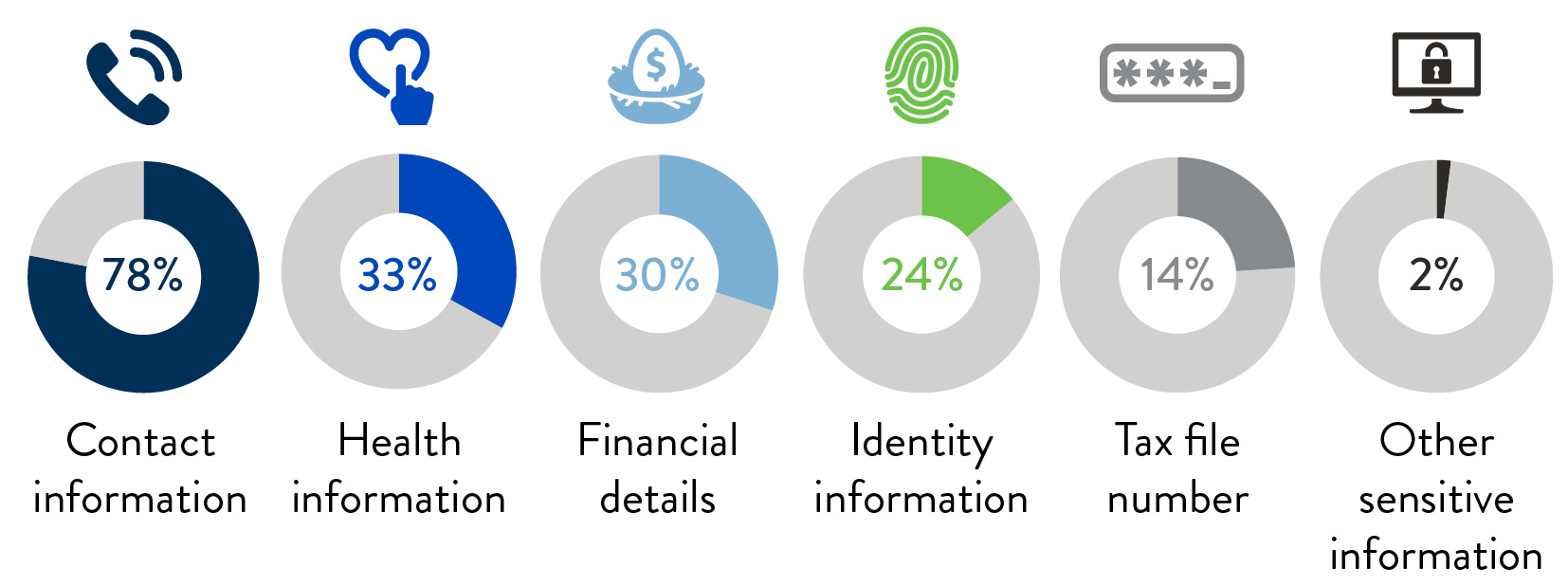
Kinds of personal information compromised
Under the NDB scheme, an eligible data breach may involve one or more kinds of personal information. Approximately 78% of all notifications involved contact information, such as an individual’s name, email address, home address or phone number. The OAIC distinguishes ‘contact information’ from ‘identity information’, which it defines as information used to confirm an individual’s identity such as their drivers licence number or passport number.
Health information accounted for 33% of all notifications, followed closely by financial details (i.e. an individual’s bank account or credit number, 30% of all notifications), identity information (24% of all notifications), tax file number (14% of all notifications) and other (non-health) sensitive information (2% of all notifications).
Source of the data breach
Just over half of all notifications involved human error, including inadvertent disclosures. Similarly, in the 2016–2017 financial year, 46% of all voluntary notifications were reported to be the result of human error. Malicious or criminal attacks such as theft of personal information following unauthorised access to an entity’s systems accounted for 44% of all sources of notified data breaches.

Number of individuals affected by the data breach
Over half of all notifications involved the personal information of between 1 and 9 individuals, and only 5% of breaches involved the personal information of more than 10,000 individuals.

Visit SmartCounsel
