2021 will see APRA dial up its supervision and scrutiny of regulated entities’ cyber risk management. This includes a more targeted approach to enforcing compliance with prudential standard CPS 234 as APRA seeks to ensure the cyber resiliency of Australia’s financial sector.
In his speech at the Financial Services Assurance Forum on Thursday 26 November 2020, Executive Board Member, Geoff Summerhayes unveiled APRA’s new Cyber Security Strategy for 2020 to 2024 (see our article Australia’s Cyber Security Strategy 2020: What you need to know) which includes a tough new approach on CPS 234. Summerhayes cites the risks of remote working in response to Covid-19, increasing digitisation, complex chains of services providers as well as the continued evolution of cyber threats, as driving this tough new approach.
The full speech is available - Executive Board Member Geoff Summerhayes - speech to Financial Services Assurance Forum
APRA’s cyber security strategy
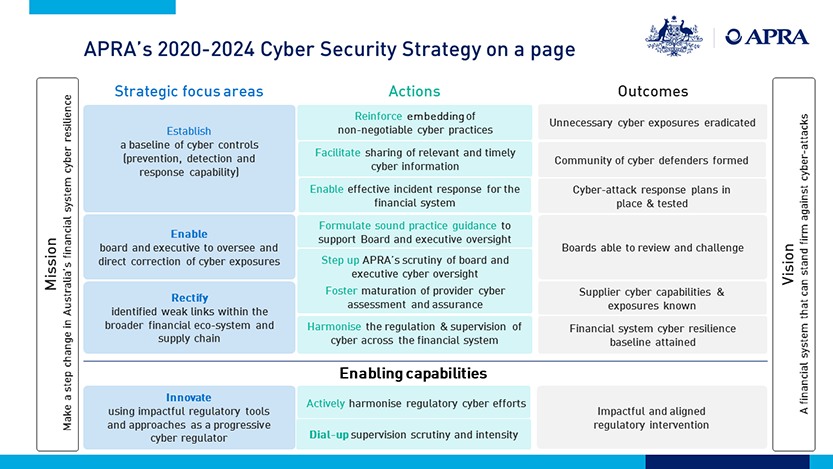
The 2020-2024 Cyber Security Strategy is summarised in the diagram below:
In his address, Summerhayes described APRA’s new strategy as a ‘step change in regulatory intervention’. Describing APRA’s observations to date, he stated that all regulated entities won’t be fully compliant when the third party obligations of CPS 234 come into effect on 1 January 2021. Of the 680 entities which APRA regulates, around 100 have requested extensions of time to address shortcomings.
Even where entities have reported compliance, technical assessments conducted by APRA to verify those reports have discovered significant weaknesses in areas such as testing programs, control environments and incident response capabilities.
APRA is also concerned that Boards either aren’t properly informed about the true state of their cyber security, or they fail to grasp the magnitude of the risks and the urgency required.
APRA has observed the following behaviours:
- cyber exposures reported to audit committees which failed to act or don’t know how to;
- audit committees struggling to interpret the severity of cyber risk findings compared with risks in other areas of the business; and
- internal auditors failing to sufficiently investigate the state of cyber security controls.
Specific measures announced by APRA
In response to the observations above, APRA has announced the following measures that it will look to implement in the new year. While some of these measures are geared towards education and leadership, others clearly show that APRA intends to hold entities accountable where they fail to meet the minimum requirements:
- APRA will formulate enhanced cyber guidance for board members, internal auditors and risk management professionals. The aim of this is to empower stakeholders to direct and implement corrective action where necessary. APRA says it intends to partner with relevant professional bodies, such as the Australian Institute of Company Directors and Risk Management Institute of Australasia, to develop this guidance.
- APRA will collect more data to better understand cyber threats and share this knowledge with the industry to enable self-assessment and benchmarking. Here, APRA intends to partner with academia to research issues such as measuring and benchmarking cyber resiliency and sharing threat intelligence with other regulators to better inform actions in the financial services sector.
- APRA will develop stronger third-party assessment and assurance practices to help regulated entities vet and monitor their suppliers. The aim of this work will be to raise the level of maturity in supplier procurement and oversight to ensure confidence in third party suppliers who manage information assets on behalf of entities.
- APRA will require certain entities to obtain independent cyber security reviews with the results provided to both the entity and to APRA. APRA refers to this as “one-off tripartite security reviews”. The particular entities who will be subject to this review are yet to be named, but it is a clear signal on APRA’s part that it will no longer accept entities representations as to compliance, it is going to require verification going forward.
- APRA regulated-entities that fail to comply with CPS 234 may be issued with a breach notice and required to create a rectification plan. If Boards are unwilling or unable to make the required changes in a timely manner, APRA may commence a formal enforcement action.
These measures are being supported by the allocation of additional funding to APRA, as announced in the most recent Federal budget.
Preparing for 2021
Based on the 2020-24 strategy and Summerhayes’ speech, it is clear that APRA will be making cyber security a priority for 2021. This includes a number of specific measures which are likely to keep a number of stakeholders within financial entities busy. APRA has made it clear that it may pursue enforcement options if deficiencies are identified in its review process.
Entities should be on the lookout for APRA to engage with the industry on cyber security matters. We expect valuable insights will be gained from this which will inform the way cyber compliance evolves over the coming months and years.
This speech makes it clear that CPS 234 will soon be subject to APRA’s so called “constructively tough” enforcement philosophy.
Given the high prevalence of entities reporting compliance but then being found to be lacking in certain areas, now is the time the revisit cyber controls to ensure continued compliance. APRA’s concern that cyber risks aren’t adequately understood or responded to also suggests that cyber literacy among stakeholders could be improved.
For further information about the obligations under CPS 234, see CPS 234: 8 things you didn’t know about APRA’s new cybersecurity standard.

Visit Smart Counsel
