The Notifiable Data Breaches scheme (NDB) (February 2018), enacted new obligations for both government agencies and private sector organisations that were already subject to the Privacy Act 1988 (Cth). One year on from the scheme’s introduction, the Office of the Australian information Commissioner (OAIC) reports that data breach notifications have increased by over 700%.
The NDB imposes a legal requirement on those agencies and organisations to undertake a review whenever they suspect that there may have been loss of, unauthorised access to, or unauthorised disclosure of personal information they hold. If a serious harm is likely to result, then the entity must notify both the affected individuals, and the OAIC. For more details on your obligations under the NDB, see our previous insight.
The rationale? Transparency, accountability and ultimately harm minimisation.
NDB snapshot
Previously, reporting of data breaches was voluntary, with reported breaches totalling an average of 127 reports per year. In the year 1 April 2018 to 31 March 2019, there have been almost 1000 reported breaches, an increase of 712% on the previous year. So now that the data is in, what have we learnt?
Gone phishin’
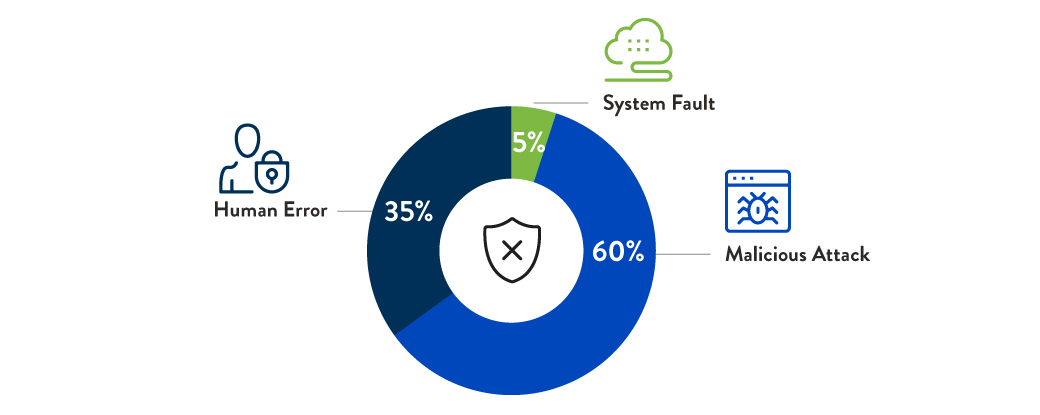
Malicious attacks formed 60% of total reported breaches in this period. Of these, ‘phishing’ (the process of fraudulently gaining someone’s credentials via a fake login portal, link or website that users would otherwise consider trustworthy) accounted for 153 of 394 breaches (39%).
Reply all
Coming in second is good old human error. Of the 340 total breaches that were the result of human error, 97 were instances of simply sending information to the wrong recipient (29%).
Industry leaders
Health service providers comprised 36% of reported breaches, with finance (25%) and legal, account and management services (18%) coming in next.
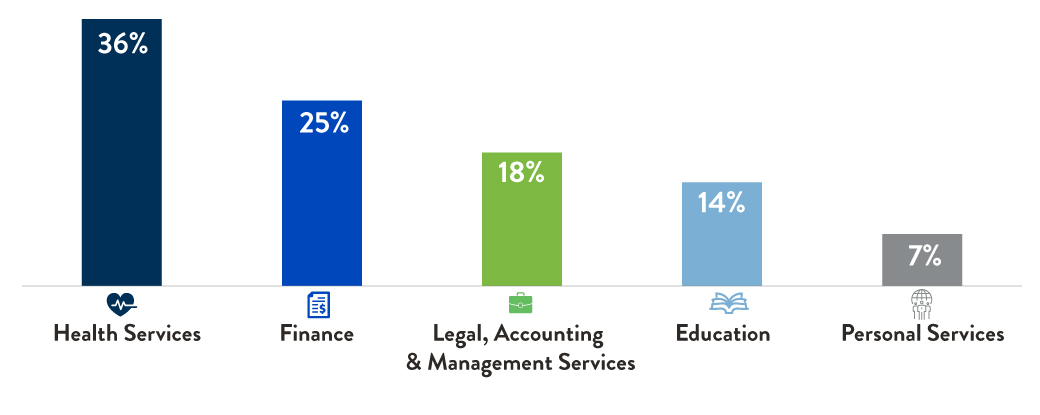
The OAIC notes that these industries consistently top the list due to the scale of their holdings, the volume of data processing undertaken, and their preparedness to report breaches. Health services as the leading industry reporter is consistent with international trends and, perhaps most notably within this sector human error actually outweighs malicious attacks as the leading cause of data breaches (55%).
Can I have your number?
When it comes to the type of information breached, contact details top the list, with financial details coming in second.
While lost contact information may not result in immediate or financial harm, it is commonly seen as the first step in the wider phishing process and can lead to more serious ramifications in the future.
Interestingly, despite the health sector topping the list of reports by industry, health information only accounts for 12% of actual breached data.

Recommendations
The value this data holds is primarily in its ability to help mitigate future breaches. Here are the top OAIC recommendations to data-holding entities:
- Educate users on email-based threats (such as detection of phishing emails), password management and use of third-party data protection services;
- Implement multi-factor authentication and anti-spoofing controls;
- Implement dedicated training programs aimed at data security and threat identification;
- Invest in preventative technologies and processes (such as encryption, secure data transfer and monitoring systems);
- Prepare for data breach incidents with an incident response plan and regular exercises or data breach simulations (you can view OAIC’s “Data breach preparation and response guide” here);
- Assess your data holdings and the potential impact a breach would have on customers; and
- Establish and maintain microsites or support lines to effectively communicate with customers after a breach has occurred.
Conclusion
While the OAIC recognises that there is room for improvement when it comes to the more complex issues of navigating multi-party and multi-jurisdictional breaches, it is clear that there has been an overall increase in general awareness and transparency arising from the NDB. Although just a start, it is insights like these that help entities adapt and respond in a continually evolving technology landscape.
You can also check out the G+T guide to ensuring your contracts are NDB compliant, or alternatively, if you are an individual affected by a breach you can visit the OAIC’s ‘data breach guidance’ page here for steps you can take to protect yourself.
Prepared by Alexander Ryan, Melissa Fai and Lesley Sutton

Visit Smart Counsel
